IoT In Manufacturing: Device Communication & Network Security

The Internet of Things (IoT) is transforming manufacturing, helping to drive innovation, reduce costs, detect and report machine faults earlier, improve the quality of products, and shorten time to market.
IoT systems use a network of sensors, devices, applications, and networking equipment to collect, monitor, and analyze data from manufacturing operations. Therefore, smart factory operators must invest in a robust network architecture that protects the integrity of data shared between sensors, devices, and cloud services.
Networking fundamentals in IoT-enabled manufacturing
Networking is the backbone of IoT in manufacturing. Sensors and connected devices and equipment rely on it to communicate with each other, share data, and coordinate.
However, networking in IoT isn’t just about connecting devices; it’s about ensuring secure, reliable, and fast communication across all levels of the manufacturing process. It’s the silent enabler that makes all the smart stuff possible.
Connectivity options for IoT systems in manufacturing are vast, from Wi-Fi to cellular to specialized IoT networks like LoRaWAN. Each has its pros and cons. For instance, Wi-Fi offers high-speed data transfer but usually consumes more power.
Alternatively, LoRaWAN is perfect for long-range communication with low data rates, making it ideal for remote monitoring. Consider a factory environment where various equipment needs to communicate. This can be done using a mix of Wi-Fi for high-speed, local data transfer, and LoRaWAN for long-distance communication.
Security is a fundamental networking concern in IoT systems deployed in factories. A poorly secured network can be a target for hackers, who can bring a whole production line to a halt simply by corrupting a few sensors.
Robust networking ensures data integrity and quick fault detection. Interoperability is another crucial attribute of a sturdy networking architecture. Different machines and devices need to speak the same language. Protocols like MQTT and CoAP come in handy here, with the former especially effective for low-bandwidth, high-latency environments.
Equally critical for an IoT-powered factory is the real-time transmission of data. With 5G networks, data transmission speeds are blazing fast, allowing near-instantaneous data transfer. This is especially beneficial in scenarios like real-time product enhancement, where immediate feedback and adjustments can be made to products even after they leave the production line.
IoT devices in manufacturing
IoT devices are revolutionizing manufacturing, making factories smarter, more efficient, and more responsive. They enable real-time data collection and analysis, which transforms production lines into efficient, automated powerhouses.
Smart sensors
Smart sensors are devices that capture information from the physical environment and use embedded microprocessors to electronically process, exchange, store, or transmit it so the system can perform predefined tasks. These tiny devices measure everything from temperature and humidity to vibration and pressure.
For instance, in an automobile manufacturing plant, smart sensors can continuously monitor the vibration levels of assembly line machinery. If a sensor detects abnormal vibrations, it can automatically trigger maintenance before the machine breaks down, preventing costly delays.
Edge devices
Edge devices are the brains in any IoT setup, positioned between the sensors and the cloud, processing data locally. Their central positioning enables faster decision-making and reduces latency. They also help conserve bandwidth by ensuring that only relevant data gets sent to the cloud.
In a food processing plant, edge devices can analyze data from various sensors to ensure that environmental conditions remain optimal for food safety. If the temperature in a storage area goes above a certain threshold, the edge device can instantly turn on cooling systems without waiting for instructions from the cloud.
Edge devices aren't just limited to simple controls. They can run complex algorithms using frameworks like TensorFlow Lite to perform real-time image recognition, helping with quality control on production lines. Here’s a snippet code example in TensorFlow Lite:
Cloud solutions
Cloud solutions play a pivotal role in IoT systems for manufacturing. They are crucial for storing and processing large amounts of data collected from various sensors.
Imagine a factory with thousands of sensors, each generating data every second. The cloud can handle this influx, using services like AWS IoT or Azure IoT Hub to provide real-time analytics and insights. For example, AWS IoT Analytics can help manufacturers pinpoint inefficiencies in the production process by analyzing data trends over time.
Human-machine interfaces (HMIs)
HMIs let factory operators interact with the IoT system. An HMI might display the real-time status of all machinery in a plant, showing alerts for any anomalies.
For example, an HMI screen could show a dashboard with temperature and humidity readings from various storage facilities, helping managers ensure optimal conditions for their products.
IoT gateways
IoT gateways act as the bridge between IoT devices and the cloud or on-premises servers. Their main job is to aggregate, filter, and process data before sending it on. This is vital for reducing latency and ensuring that only relevant data is sent to the cloud for further analysis.
When running a manufacturing plant with hundreds of sensors monitoring everything from temperature to machine vibrations sending every piece of raw data directly to the cloud could overwhelm your network and slow down decision-making. Instead, an IoT gateway can pre-process this data, performing initial analytics at the edge.
If a temperature sensor detects readings within the normal range, the gateway can simply ignore this data. But if the temperature spikes beyond a set threshold, the gateway might send an alert to the cloud, triggering immediate actions like cooling system adjustments or technician inspections.
IoT gateways also boost security by encrypting data and ensuring it’s transferred securely, preventing unauthorized access. Some IoT systems allow you to run local compute, messaging, data caching, and sync capabilities for connected devices securely. You can even deploy machine learning models on these gateways to make intelligent decisions right at the edge.
IoT cloud services
The cloud stores, processes, and analyzes the data generated by smart sensors on the production line, making it accessible for insights that drive informed decisions.
AWS IoT, for example, offers a suite of services tailored to manage IoT devices and data securely and at scale. As well as AWS Core which connects your devices to AWS, AWS IoT also provides AWS IoT Analytics for deep data analysis and AWS IoT Events for event monitoring, so you can detect and respond to changes in your manufacturing environment in near real-time.
Microsoft, through Azure IoT, and Google, through Google Cloud IoT have their own cloud platforms for IoT devices that deliver similar functionalities to varying scales. Azure IoT facilitates bi-directional communication between IoT applications and the devices it manages, while Google Cloud IoT is designed for scale and efficiency.
IoT communication protocols
IoT communication protocols determine how data is transmitted between devices, sensors, and cloud platforms. Having the right protocol can make all the difference in ensuring your IoT implementation is efficient and reliable.
Message Queuing Telemetry Transport (MQTT)
MQTT is a lightweight messaging protocol that's perfect for IoT because it uses minimal bandwidth and is excellent for unreliable networks. It works on the publish-subscribe model, making it convenient for real-time updates.
For example, you can use MQTT to have sensors on an assembly line publish data about temperature and humidity, and then have an edge device subscribe to these updates to perform real-time monitoring.
Here's a simple code snippet showing how MQTT works using the `paho-mqtt` library in Python:
CoAP (Constrained Application Protocol)
CoAP is another lightweight protocol but is specifically designed for constrained devices and networks. It uses UDP for data transmission and is ideal for devices with limited processing power.
For instance, CoAP can be used in a predictive maintenance system where low-powered sensors on machinery report their status to a central server.
Here's an example using `aiocoap`, a Python library for CoAP:
HTTP/HTTPS
While not specifically designed for IoT, HTTP and HTTPS are widely used due to their simplicity and the vast infrastructure already in place. They are particularly useful for IoT devices that need to interact with web services.
Unilever's digital twins, for example, could use HTTPS to send data securely to cloud-based analytics platforms. Using Python's `requests` library, sending data over HTTPS might look like this:
Zigbee
Zigbee is a specification for high-level communication protocols using low-power digital radios. It's often used in applications that require low data rates and long battery life, like remote monitoring systems. Zigbee's mesh network capability ensures robust and reliable communication across numerous devices in a factory setting.
Z-Wave
Z-Wave is similar to Zigbee but often finds its niche in home automation. However, its reliability and range make it adaptable for smaller-scale industrial applications. For example, Z-Wave can be used to control lighting and HVAC systems within a manufacturing site, ensuring optimal working conditions without manual intervention.
LoRaWAN (Long Range Wide Area Network)
LoRaWAN is designed for long-range, low-power communication, making it ideal for IoT applications that need to cover large areas, such as tracking assets across a sprawling factory complex. LoRaWAN can transmit data over distances of up to 10 kilometers, making it perfect for large-scale IoT deployments.
Each of these protocols has its strengths and weaknesses, and the choice depends on your specific use case. Whether it's MQTT for real-time updates, CoAP for constrained devices, or LoRaWAN for long-range communication, you have many options to ensure your IoT implementation in manufacturing is both effective and efficient.
Network eavesdropping on IoT devices
Network eavesdropping is where threat actors intercept and read data packets as they travel across the network. This can cause data breaches and expose sensitive information.
Picture smart sensors on an assembly line transmitting real-time data about machine performance. If an attacker intercepts this data, they can gain insights into your manufacturing processes and even inject false data to disrupt operations.
One way we can protect against network eavesdropping is by using encryption protocols like TLS (Transport Layer Security). Encrypting data ensures that even if someone intercepts the packets, they can't read the content.
In manufacturing, we can also deploy Virtual Private Networks (VPNs) to shield communication between devices. A VPN creates a secure tunnel over the internet, ensuring data integrity and privacy. By encrypting all traffic between IoT devices and the central servers, VPNs can thwart many eavesdropping attempts.
Another effective measure is network segmentation, which involves dividing the network into multiple smaller sub-networks. This way, even if an attacker gains access to one segment, they cannot easily move laterally across the network. Network segmentation minimizes the potential impact of an attack and confines the threat to a limited area.
Furthermore, implementing network monitoring tools can help detect suspicious activity. Tools like Wireshark or specialized IoT security solutions can monitor network traffic for any anomalies. By analyzing traffic patterns and flagging irregular activities, these tools provide early warnings for potential eavesdropping attempts.
Ensuring regular software updates and patch management is crucial. IoT devices often run on firmware that can have vulnerabilities. Regular updates help patch these vulnerabilities, making it harder for attackers to exploit them. Automated patch management systems can be used to streamline this process, ensuring devices are always up-to-date without manual intervention.
Man-in-the-Middle Attacks
In a Man-in-the-Middle (MitM) attack, a malicious actor intercepts and possibly alters the communication between two parties without their knowledge.
Let's say your predictive maintenance system is sending sensor data to the cloud for analysis; if an attacker intercepts this data, they could manipulate it to trigger false alerts or hide real issues, causing equipment failure and unsafe working conditions.
The danger doesn't end there. MitM attacks can also target IoT-enabled energy management systems. If an attacker intercepts the communication between energy sensors and the central monitoring system, they could manipulate data to create false alarms or hide peak loads. This would result in inefficient energy management, increased costs, and potential equipment damage.
To protect against MitM attacks, implementing secure communication protocols is crucial. For example, Transport Layer Security (TLS) and Secure Sockets Layer (SSL) can encrypt data between IoT devices and servers, making it far more challenging for attackers to intercept and tamper with the data.
The code snippet above establishes a secure connection between a client and server, ensuring data integrity and confidentiality. Using TLS or SSL is essential for safeguarding any IoT-based communication, especially in manufacturing environments where data accuracy and security are critical.
MitM attacks can also exploit poorly secured Human-Machine Interfaces (HMIs). If an attacker gains access to an HMI, they could manipulate the data shown to operators, leading to incorrect decisions. For instance, altering the performance metrics displayed on the HMI could make it seem like machines are operating efficiently, while they’re on the brink of failure.
Sinkhole Attacks
An example of a sinkhole is where a malicious node advertises an optimal route to attract all the traffic in the network. Once the data is funneled to this node, the attacker can drop packets or manipulate the data.
Sybil Attacks
Sybil attacks involve a single node presenting multiple identities to other nodes in the network. This can severely disrupt the routing protocols. For instance, suppose a single rogue device in a manufacturing environment pretends to be several sensors. It could manipulate network traffic, introduce delays, or even provide false data.
Wormhole Attacks
Wormhole attacks involve an attacker recording packets at one location in the network and tunneling them to another location, where they are replayed. This can cause data packets to traverse through unintended routes, bypassing security measures.
Consider a factory where data from a temperature sensor is tunneled through an attacker's node before reaching the control system. This could result in incorrect environmental readings, potentially leading to unsafe conditions.
Practical approaches for securing IoT systems in manufacturing.
Routing attacks and networking eavesdropping events can devastate smart manufacturing by disrupting not just data flow but operational efficiency. Employing robust security measures, including encrypting communication channels, authenticating devices, and continuously monitoring network traffic, helps mitigate these risks.
Investing in secure IoT architecture is not just a technical necessity but a strategic business decision to safeguard manufacturing operations.
Industrial Internet Consortium (IIC)
Collaboration between industry leaders is key to advancing IoT in manufacturing. The Industrial Internet Consortium (IIC) is a prime example of this collaborative effort.
The IIC, a global organization founded by major companies like GE, IBM, and Intel, focuses on accelerating the growth of the Industrial Internet of Things (IIoT). This consortium brings together industry, academia, and government to break down technology barriers and drive standards and best practices for the industrial IoT ecosystem.
One of the IIC’s significant projects is the Testbed Program, which provides experimental platforms where Industrial IoT applications can be developed, tested, and validated. For instance, the 'Smart Factory Web' testbed brings together multiple factories in different locations to create a network of smart production facilities.
By leveraging IoT, these interconnected factories can share data in real time, optimizing production schedules and inventory management across the entire network. Imagine a factory in Germany needing a specific part that another factory in the U.S. has in surplus. Using IoT-enabled data sharing, this part can be quickly identified and shipped, reducing downtime and increasing efficiency.
The IIC also emphasizes security, a critical concern in IIoT. They have developed the "Industrial Internet Security Framework (IISF)," a guideline that provides comprehensive security best practices for industrial IoT systems.
Another exciting initiative from the IIC is the "Digital Twin Interoperability" testbed. This project focuses on creating digital twins—virtual replicas of physical assets—that can communicate and interact with each other.
For example, a digital twin of a machine on a production line can predict when maintenance is needed by analyzing real-time data from IoT sensors. This predictive maintenance approach helps in reducing unexpected machine downtimes and extending the machinery's lifespan.
Using VPNs and SD-WAN to boost network security in IoT-enabled factories.
Virtual Private Networks (VPNs) and Software-Defined Wide Area Networks (SD-WAN) help ensure data transmitted between IoT devices and central systems is both secure and efficient.
VPNs create a secure tunnel over the internet, encrypting data to keep it safe from prying eyes. When you have IoT sensors scattered across a manufacturing plant, VPNs can make sure all the data they generate travels securely to your central server.
For instance, if you have a factory monitoring system sending real-time quality assurance data, a VPN will encrypt this data, ensuring it’s not intercepted during transmission.
SD-WAN technology optimizes the performance and security of applications by using software to control the WAN connections. Unlike traditional WANs, which use fixed connections like MPLS, SD-WAN dynamically routes traffic based on the best performance and security criteria. This is essential for IoT in manufacturing, where data from various sources needs to be transmitted quickly and securely.
For example, let’s say your smart sensors are tracking the temperature and humidity across different sections of a factory floor. With SD-WAN, you can prioritize this critical data, ensuring it gets to your central system promptly.
If one path becomes congested, SD-WAN will automatically reroute the data through a less congested path, maintaining performance and reliability.
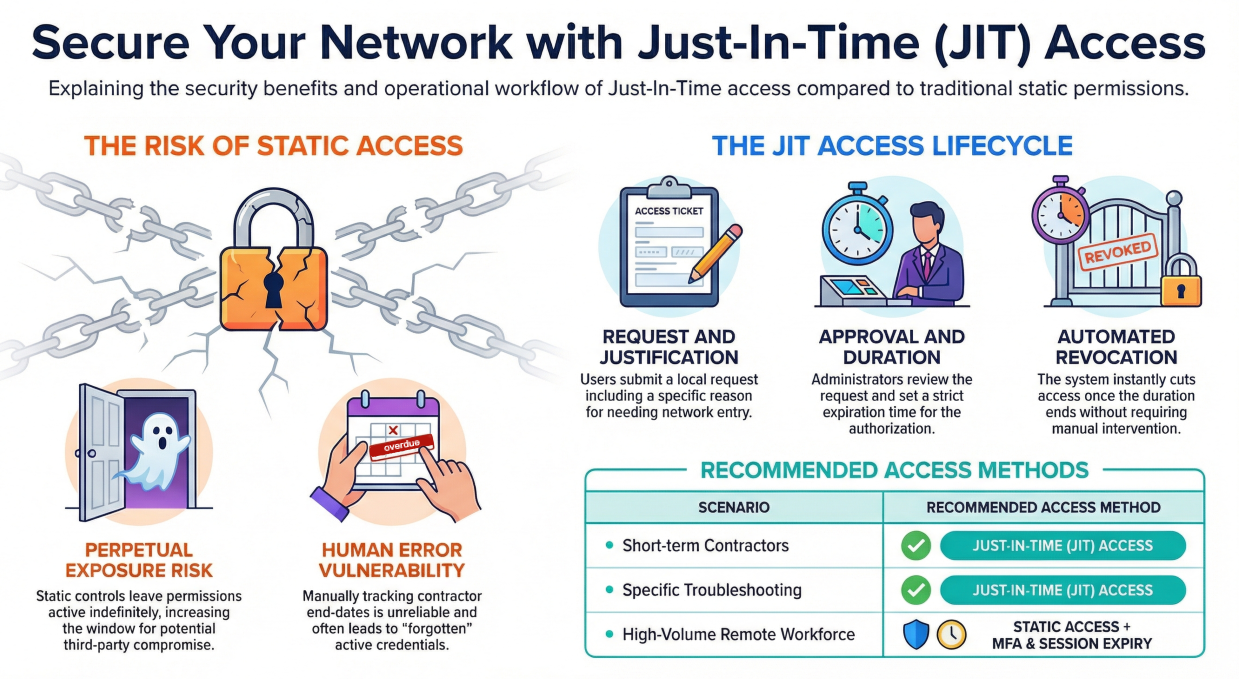
Zero Trust Architecture (ZTA) in IoT
Zero Trust Architecture offers a comprehensive way to secure IoT devices in manufacturing. Unlike traditional security models, which assume that everything inside an organization's network is trustworthy, ZTA operates under the principle of "never trust, always verify." This means every device, user, and network component must continually prove its trustworthiness.
To start, you need to ensure secure authentication for every IoT device. For example, using multi-factor authentication (MFA) can add an extra layer of security.
Devices should not be granted access based solely on network location. Instead, they should provide valid credentials and pass stringent checks every time they attempt to communicate with other devices or systems.
Monitoring and auditing are also critical in a ZTA environment. Consider using continuous monitoring tools to detect any unusual activities on a production line. For instance, if an IoT sensor in a factory suddenly starts communicating with an unknown server, that should raise a red flag.
Another important aspect of the Zero Trust architecture in IoT is micro-segmentation. By dividing the network into smaller, isolated segments, you minimize the risk of lateral movement by attackers.
For example, if a threat actor gains control of an IoT sensor, micro-segmentation ensures they cannot easily access other critical components like robotic arms or assembly line controllers.
A zero-trust approach also emphasizes secure data practices. Encrypt data both in transit and at rest. This step ensures that even if an attacker intercepts the data, it remains unreadable.
The last crucial aspect of the Zero Trust architecture in IoT is applying the least privilege access network security dimension. Only give devices the minimum access they need to perform their functions.
For example, a sensor that only needs to send temperature data should not have permission to access or modify other system configurations. Implementing role-based access control (RBAC) can help in enforcing these principles effectively.
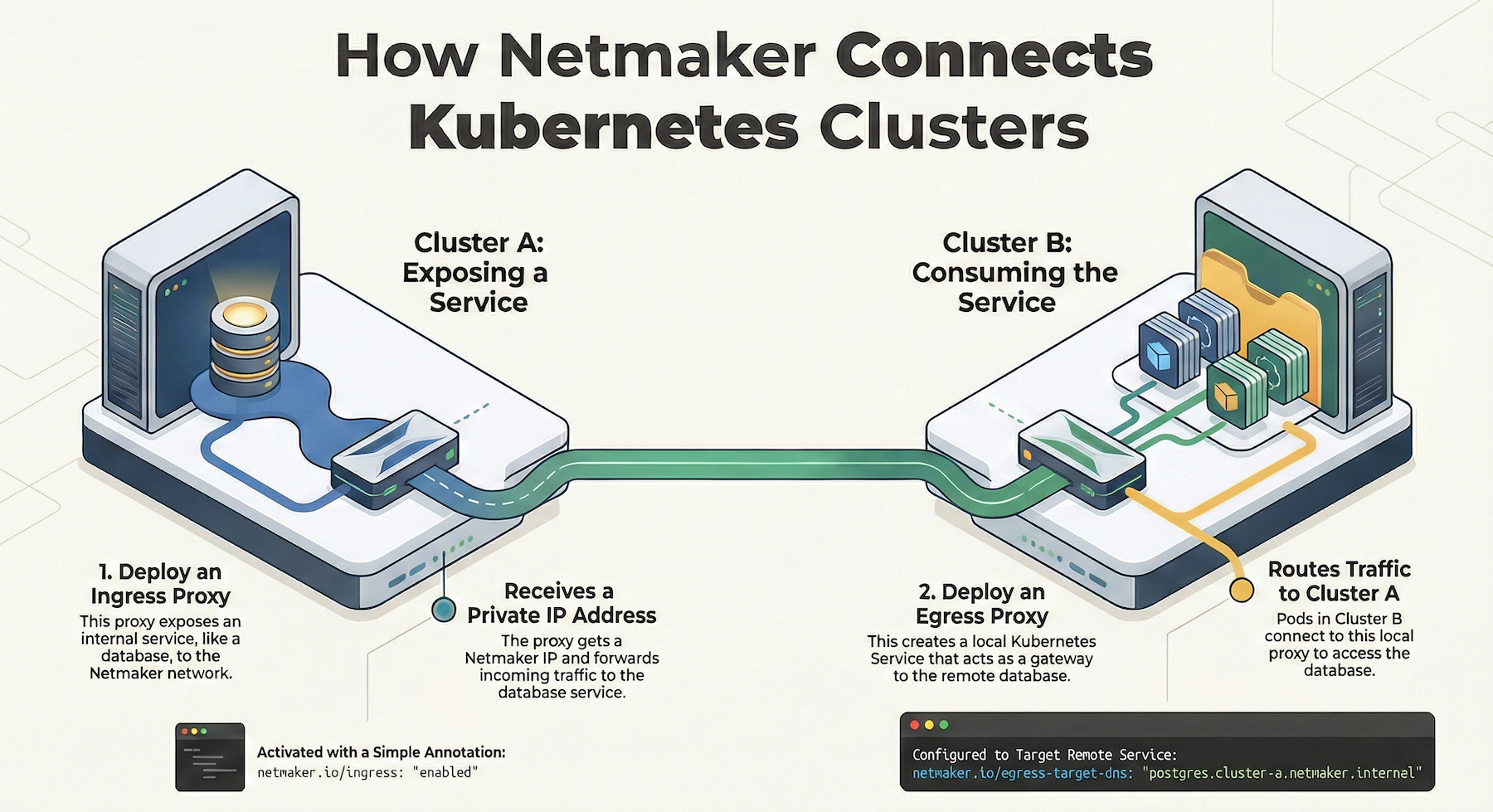
Enhancing IoT in Manufacturing with Netmaker
Netmaker offers a comprehensive solution to enhance device communication and network security in IoT-enabled manufacturing environments. By providing a secure virtual network, Netmaker ensures that data transmitted between IoT devices and sensors is shielded from potential threats. This is achieved through WireGuard® encryption, which is integrated into Netmaker's architecture to offer high-speed, encrypted data channels that are crucial for maintaining the integrity of information shared across manufacturing processes. Furthermore, by leveraging Netmaker's mesh networking capabilities, manufacturing facilities can achieve efficient device communication without the limitations posed by traditional networking setups, allowing seamless data transfer and coordination across various equipment and sensors.
In addition to security, Netmaker enhances the scalability and flexibility of IoT networks in manufacturing. As factories expand or modify their operations, the need for adaptable network solutions becomes paramount. Netmaker supports dynamic network scaling, allowing manufacturers to add or remove devices with ease, all the while maintaining optimal network performance. The platform’s compatibility with Docker and Kubernetes further aids in deploying and managing network components efficiently, making it an ideal choice for manufacturing environments that require robust and reliable networking solutions. To start leveraging these benefits, sign up at Netmaker and transform your IoT architecture today.
.svg)





.svg)