Remote Access to a Private Azure Windows Server with WireGuard and Netmaker

Intro
If you use Azure, you may deploy resources that you don’t want to expose publicly. For instnace, a Windows Server. In these scenarios, the resource will be contained in an Azure Virtual Network and Subnet. But how do you access these resources remotely from your devices?
Azure has their own remote access VPN solution called “Azure VPN Gateway”. However, this can be unnecessarily expensive. With several users and endpoints, you can easily spend hundreds of dollars per month.
Luckily, it is pretty easy to build an alternative to Azure VPN Gateway using WireGuard® and Netmaker for free. Follow these steps, and you should be up and running in about 30 minutes.
By the end of this tutorial, you will have a gateway device running on Azure, which you can use to access your private Azure resources using a WireGuard VPN client.
Scenario

In our example scenario, we have Windows Server 2019 Datacenter running on Azure, which is only accessible via RDP over the Virtual Network subnet address (10.0.0.4). We want RDP access to the server using this address.
For your setup, this could be any private IPs or subnets on Azure, as long they are accessible from the gateway device, which we will set up next.


Step 1: Deploy the Gateway Device
Deploy a device in Azure to act as your VPN gateway. We recommend using the latest Ubuntu on the smallest possible instance type, since it is not resource intensive. However, any linux distro or instance type should work.
This device must have access to the target devices or subnets, so add it to the same subnet. Reminder, make sure the Inbound Port rules on the target device or subnet will allow traffic from the gateway device.
Lastly, the device must be accessible over the WireGuard port, which by default for Netmaker is 51821, so open 51821/udp from Any source in the Inbound Port Rules (we’re doing 51821–51830/udp to be on the safe side), and make sure it has a Public IP Address.

Gateway Device Requirements:
- Device Type: VM or Container (VM recommended)
- OS: Linux (Ubuntu 22.04 recommended)
- Size: any
- Network Settings: Must have a public IP, be a part of the virtual network, and expose 51821/udp publicly (as well as port 22 for SSH access)
Step 2: Add Gateway Device to Netmaker
Now that you’ve deployed a suitable gateway device, you must add this device to Netmaker. You can self-host Netmaker, but to get started quickly (and for free), simply sign up at https://app.netmaker.io.
By default, your account will have a virtual network named “netmaker” and an access key, also named “netmaker”. You should use these for the remainder of the tutorial, but note that in our example and screenshots these are named “azure-gw”.
Click on the network, click on “hosts”, and then click the “Add a new host” button:


Follow the steps to add the gateway device to Netmaker: SSH to the device, download and installing the netclient, and joining the network.

Once the device is visible in your “hosts” lists, you can continue to configure the device as a Gateway.

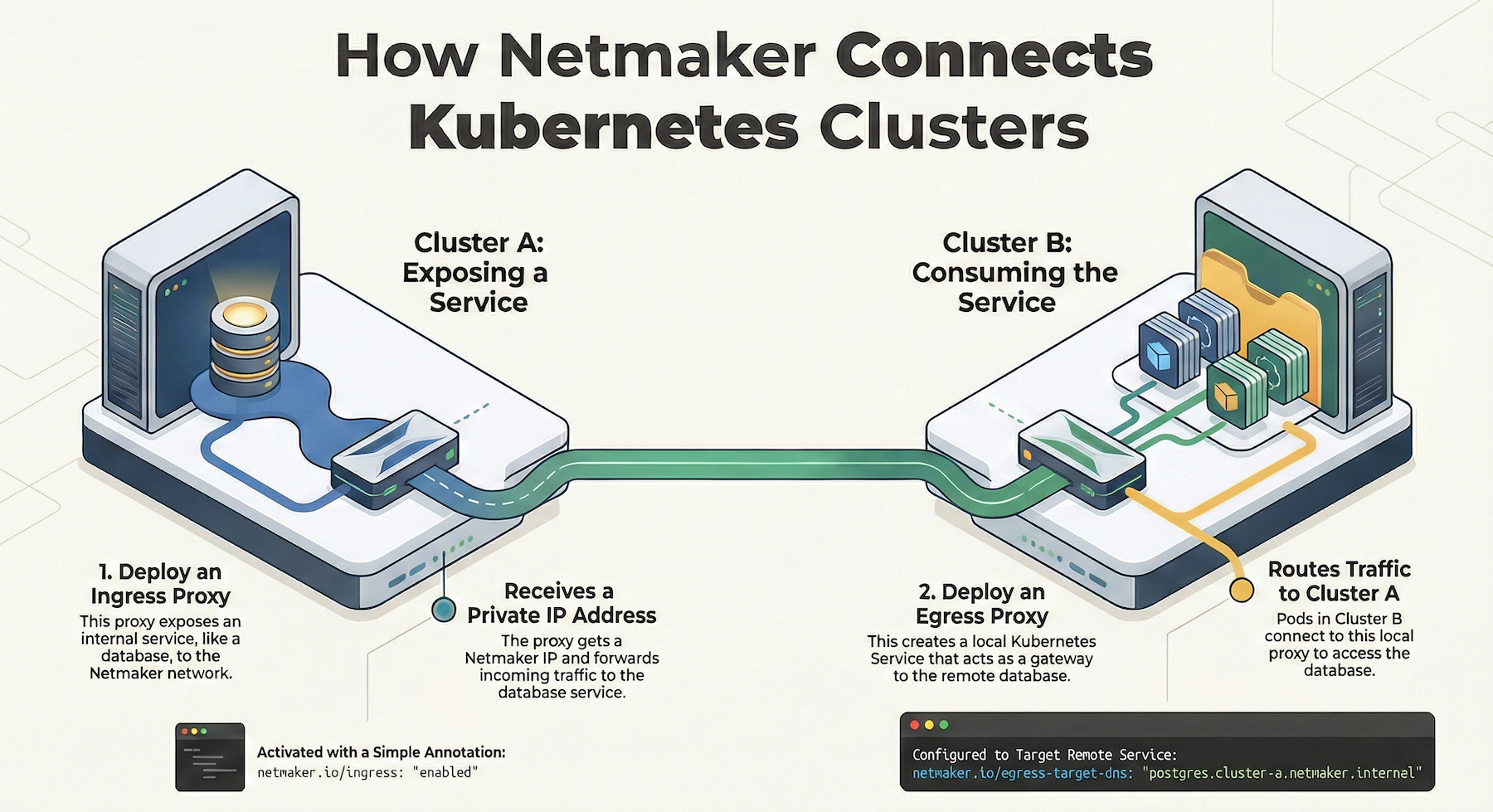
Step 3: Configure Egress

Click on “Egress” and then “Create Egress”. We will set the gateway device as an egress to the virtual network subnet range in Azure. However, we could just as easily set it to a single IP or list of IPs within the subnet.

The device is now prepared to serve traffic to the target destination.

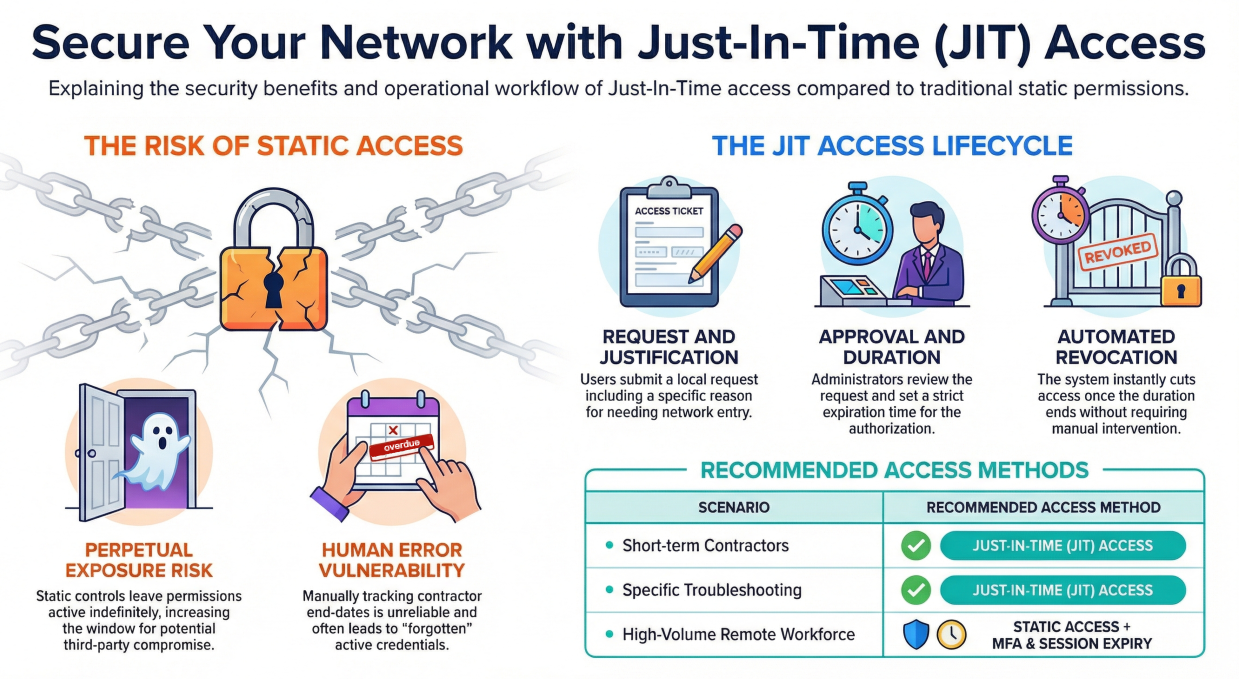
Step 4: Configure Client Gateway

The last step is to provide remote access via a “Client Gateway”. The Client Gateway simply allows you to generate WireGuard config files, which are routed through the gateway device and into the network. So, after configuring, a user will be able to reach the Egress range via the Client Gateway.
Our gateway device on Azure will act as both an “Egress Gateway”, to forward traffic to the private subnet, and a “Client Gateway”, so that it can accept traffic from WireGuard.
Click on “Clients” and then “Create Client”. Since you do not have a Client Gateway yet, it will prompt you to select a device to act as the gateway, and will generate your first client (WireGuard config file) on top of this gateway.

You can now download this config file, and run it using any standard WireGuard client.



If everything has gone correctly, you should now be able to RDP to the device using the private IP address:

You can generate additional clients as necessary, so that your gateway provides access for a whole team.
Summary
In this tutorial, we:
- Configured Azure for a remote access gateway
- Configured an Azure VM instance to act as the remote access gateway
- Generated and ran a WireGuard config file locally, to access a private Windows server via the gateway
There is much more you can do with Netmaker and WireGuard, so I hope this was a good first experience.
If you have any questions or feedback, let me know in the comments!
Enhancing Remote Access with Netmaker
Netmaker offers a robust solution for securely accessing private resources on Azure without incurring high costs associated with traditional VPN solutions. By leveraging WireGuard, Netmaker enables seamless and secure connections to Azure-hosted Windows Servers. With its capability to create mesh networks, Netmaker simplifies the process of establishing private connections across different environments. This ensures that remote access to your Azure resources is not only cost-effective but also highly secure, as WireGuard encrypts traffic with state-of-the-art cryptography.
One of the standout features of Netmaker is its ability to automate the deployment and management of WireGuard networks. This means you can quickly configure and deploy a VPN gateway on Azure, allowing authorized users to securely connect to the private network. The intuitive Netmaker UI provides an easy way to manage users, devices, and access rules, ensuring that you have full control over who can access your Azure resources. To get started with setting up a secure and efficient remote access solution using Netmaker, you can sign up here.
.svg)





.svg)