VPN Security Best Practices for Remote Companies
.png)
VPN security for remote companies comes with its own unique set of challenges. If you're a network architect or CTO in charge of your company's IT infrastructure, you understand the pain of maintaining performance and security as demands scale.
Traditional VPN setups often buckle under high loads, and the vulnerabilities they expose can feel like an open invitation to threats. In this article, we delve into the best practices that can transform your VPN from a liability into an asset. From the fundamentals to secure VPN deployment, we’ll give you a solid base to enhance your security operations.
The Importance of VPN Security for Remote Companies
Remote work is more the norm than the exception, especially since the pandemic. At that same time, however, cybercrime has surged over 600%. The stakes for robust VPN security are high, with potential risks and consequences that can severely impact any organization.
Remote work expands the attack surface dramatically and exposes your company to more sophisticated threats.
These could include:
- Data Breaches: Without stringent VPN security, companies are vulnerable to breaches that can put sensitive employee and business data at risk.
- Network Downtime: Security flaws can lead to network outages, directly impacting productivity and potentially halting business operations.
- Compliance Violations: Inadequate security measures may lead to non-compliance with data protection regulations such as GDPR or CAN-SPAM, resulting in large fines and legal complications.
- Targeted Attacks by Cybercriminals: Exploits in VPN security can make companies targets for cybercriminal attacks such as phishing or ransomware.
- Loss of Consumer Trust: Any security incident can erode trust among customers and partners.
The one common thread among all of these is the financial implications. Each one could be severe enough to bring any company down—be it fines from the government or lawsuits from angry customers.
That’s why organizations need to adopt advanced security practices and continually evaluate and adapt their strategies to mitigate these evolving risks.
VPN Security Fundamentals
Reliable VPN deployment hinges on core security principles designed to protect data integrity, confidentiality, and accessibility in a remote working environment. Here’s an overview of the foundational components:
Encryption
Encryption forms the backbone of VPN security. It’s essential for protecting data as it travels across the internet. By scrambling data into unreadable text, encryption ensures that even if intercepted, the information remains confidential. VPNs typically employ robust protocols such as IPsec or SSL/TLS to create secure connections that safeguard data.
Authentication
Strong authentication mechanisms prevent unauthorized access by ensuring only legitimate users can connect to the VPN. Methods like multi-factor authentication (MFA), which requires users to provide multiple proofs of identity, can enhance security.
Access Controls
Access control defines who can access what resources within a network. It involves managing permissions so that users have access only to the data necessary for their roles. Techniques like role-based access control (RBAC) and attribute-based access control (ABAC) are commonly used to enforce access policies to maintain the integrity and confidentiality of data.
Together, these three pillars – encryption, authentication, and access controls – create a secure VPN deployment.
VPN Protocol Selection
When selecting a VPN protocol, popular options like OpenVPN, IKEv2/IPsec, and WireGuard are the top choice:
OpenVPN
OpenVPN supports strong encryption standards, including 256-bit encryption, and is compatible with various authentication methods. It’s open-source and offers the ability to bypass firewalls and DPI (Deep Packet Inspection), making it a versatile choice for securing corporate communications.
IKEv2/IPsec
IKEv2/IPsec is known for speed and stability, particularly on mobile devices where changing network interfaces (e.g., from Wi-Fi to mobile data) is common. It supports strong encryption and has been widely adopted due to its native support on platforms like iOS and Windows.
WireGuard
WireGuard stands out for its simplicity and performance. It uses modern cryptographic techniques, such as the Noise protocol framework, ChaCha20 for encryption, and Curve25519 for key exchange. And it offers an excellent balance of speed and security. WireGuard's lean codebase allows for easier security audits and maintenance.
We recommend WireGuard as the most secure and efficient VPN protocol. It’s designed to handle high-performance needs without compromising security. And it has lower overhead so it’s less taxing on system resources, which is essential for deployments across large teams. The advantages make it an excellent choice for prioritizing fast, secure, and stable VPN connections.
Secure VPN Configuration and Deployment
The configuration and deployment of VPNs are essential for protecting sensitive data and ensuring network integrity. Here are five best practices to enhance the security of your VPN settings:
- Choose a Standards-based VPN: Opt for VPN solutions that use well-established standards like IKE/IPSec rather than those relying on custom SSL/TLS protocols.
- Implement Strong Cryptography: Use solutions that support multi-factor authentication and digital certificates.
- Regular Updates and Patch Management: Constantly monitor and promptly apply updates and patches to your VPN software.
- Restrict VPN Access: You need strict access controls to limit connections to the VPN. Use firewall rules to permit only necessary protocols and ports for VPN traffic.
- Secure and Inspect VPN Traffic: All VPN traffic needs to pass through a comprehensive security stack, including firewalls, intrusion prevention systems (IPS), and web application firewalls (WAF).
With these best practices, you can significantly fortify your VPN deployments against cyber threats.
Access Management and User Authentication
Robust user authentication mechanisms are needed to protect against unauthorized access to systems and data. Multi-factor authentication (MFA) is one of the most powerful access management tools in your arsenal.
It requires users to provide multiple forms of verification before access is granted. This typically includes something the user knows (like a password), something the user has (like a mobile device or security token), and something the user has (like a fingerprint or facial recognition).
Despite the added security, passwords are still a fundamental aspect of user authentication. Enforce strong password policies that require complexity and regular changes to keep security at its highest.
Also, make sure to regularly monitor authentication attempts and responses. Analyzing log data can help identify and respond to potential threats in real time, enhancing security postures.
And don’t forget about the human element. Regular training on the importance of security practices, including the effective use of MFA, is vital. Users should be aware of phishing attacks and other schemes that target their credentials.
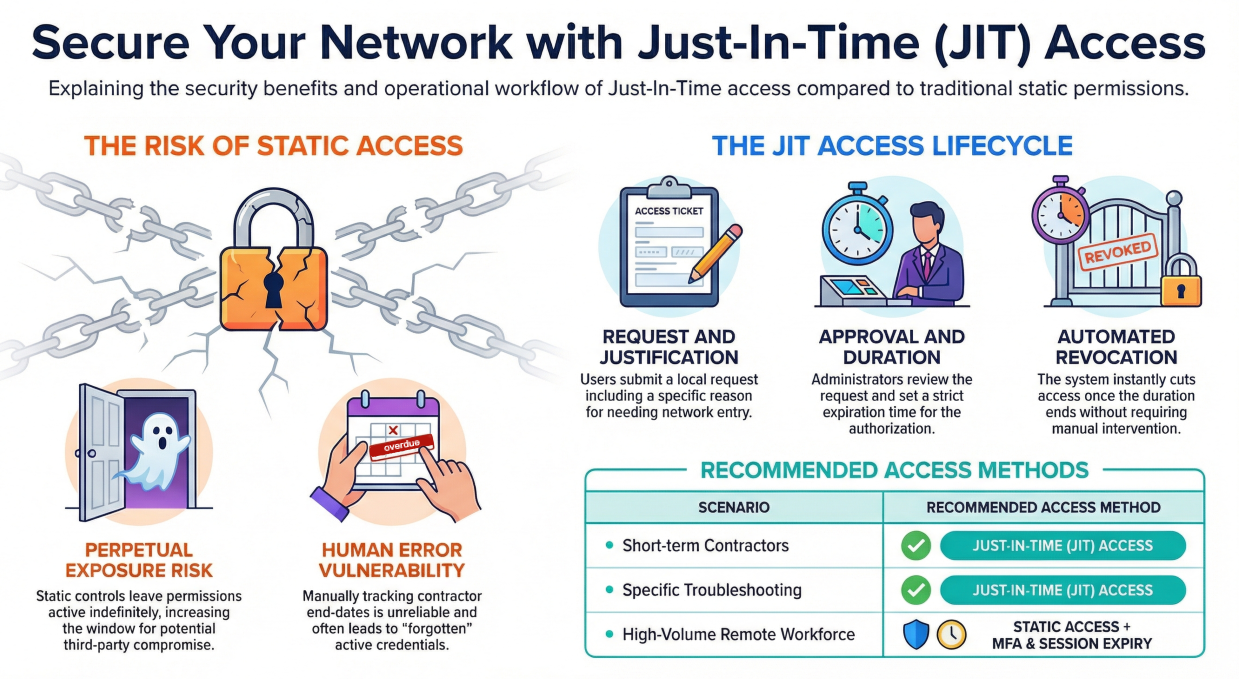
Network Segmentation and Least-Privilege Access
Two important concepts to know are network segmentation and least-privilege access:
Network Segmentation
Network segmentation enhances VPN security by dividing the network into smaller, manageable chunks. This setup restricts an attacker's access to the entire network if they compromise one segment. It's a proactive defense strategy that helps isolate security breaches and simplifies compliance management by segregating data according to security requirements.
Least-Privilege Access
The principle of least-privilege access is closely tied to network segmentation. It dictates that users and devices are granted the minimum level of access necessary to perform their tasks. And it reduces the risk of insider threats and limits the potential damage from compromised accounts. Take a zero-trust security model, where trust is never assumed, regardless of the user's location or device.
Together, they form a framework that mitigates risks by controlling how data and resources are accessed.
Monitoring and Incident Response
Continuous monitoring and logging of VPN activity are essential. With comprehensive logs, you can track access patterns, detect anomalies, and respond effectively to incidents.
Here’s what effective incident response and remediation look like in practice:
- Preparation: Establish protocols and tools in place for monitoring and logging.
- Detection: Use logs to identify unusual activities and potential threats.
- Analysis: Assess the extent and impact of the breach to inform the response strategy.
- Containment: Isolate affected systems to prevent further damage.
- Eradication: Remove the source of the breach and secure vulnerabilities.
- Recovery: Restore systems and services to normal operations safely.
- Post-Incident Review: Analyze the incident to improve future response efforts.
These steps provide a structured and efficient approach to handling security incidents that strengthen the security posture of your VPN environment.
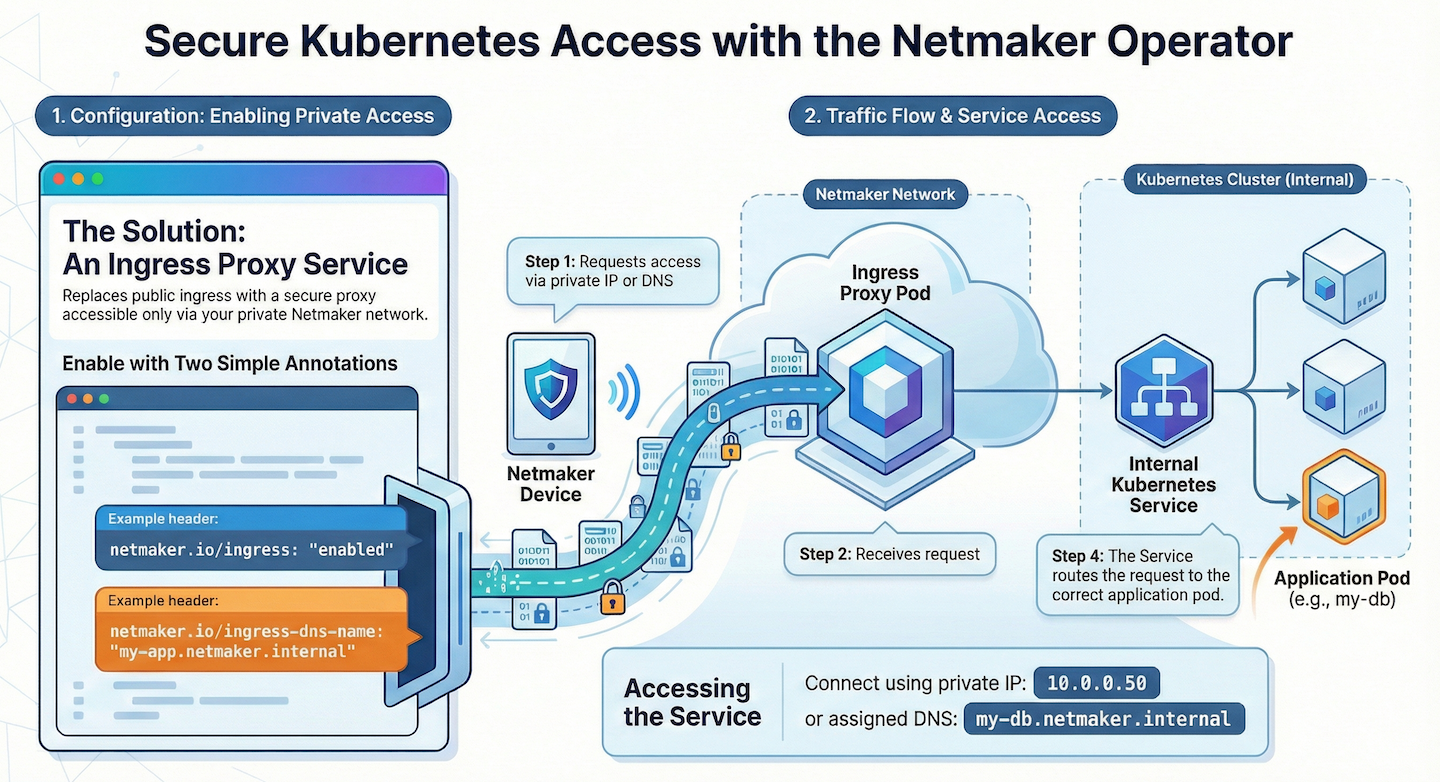
Leveraging Managed VPN Solutions
Netmaker.io stands out as a managed VPN solution for small to medium-sized businesses looking to streamline their remote network management. It offers a modern approach with a mesh VPN for secure, high-performance connections. Netmaker.io simplifies remote access with features like a Remote Access Gateway for easy network connectivity with minimal setup and integrates seamlessly with popular cloud platforms and IAM solutions for a cohesive security framework.
Why opt for a managed VPN solution?
- Enhanced Security: With strong encryption and MFA, you can be confident your data and network are protected.
- Scalability: Easily scales with the growth of your company.
- Cost Efficiency: Reduces the need for extensive in-house security infrastructure and specialized IT staff.
- Simplified Management: Automates routine tasks like deployment, configuration, and user management.
- Reliable Connectivity: Consistent and high-performance connections that are vital for business operations.
Want to learn more about Netmaker.io and how we can help empower your remote workforce? Visit our homepage to explore how Netmaker can help you secure your remote resources(or contact us for a demo by our security experts).
Enhancing VPN Security with Netmaker
Netmaker offers a robust solution to enhance VPN security for remote companies, addressing common vulnerabilities found in traditional VPN setups. With its mesh VPN architecture, Netmaker optimizes network performance and ensures secure, reliable connections, even under high loads. The platform facilitates encrypted peer-to-peer communication, minimizing the risk of data breaches and network downtime. By utilizing WireGuard as its underlying protocol, Netmaker provides state-of-the-art encryption, safeguarding sensitive business and employee data against cyber threats.
Furthermore, Netmaker's advanced access control features help companies comply with data protection regulations such as GDPR. By providing granular control over network permissions, organizations can ensure that only authorized users can access sensitive resources, reducing the risk of compliance violations and targeted attacks. For businesses looking to improve their VPN security, getting started with Netmaker is straightforward. Explore how Netmaker can enhance your company's remote network security by signing up here.
.svg)






.svg)