Taming OpenClaw: Navigating the Hazards of the Autonomous AI Assistant

Introduction
OpenClaw, previously MoltBot, previously ClawdBot, is an open source tool that promises to automate your entire life with a personal AI assistant with the power to do…anything?
It’s a fascinating, and quite frankly, scary application of LLMs. The project has exploded in popularity in recent months, even causing Mac Minis to go out of stock as users hope to host the application locally.
OpenClaw has the power to be incredibly powerful for individuals who would like an AI buddy to handle the drudgery of normal life, but it comes with incredible security risks as well. Security researchers have noted many vulnerabilities, and have discovered millions of records of exposed credentials, personal details, and private messages.
Worse, OpenClaw’s is fundamentally insecure by design, meaning there really is no way to use it safely. To provide you with a quick list, here are just some of the issues:
- No code signing for plugins
- No permissions model
- No sandboxing
- Credentials are stored in plaintext
- Uninhibited access to local files
- Open to prompt injection
Let’s summarize the security flaws this way: You’re giving a bot access to all of your personal information, with the power to do whatever it wants with that information, with insecure credentials which are easily exposed, with plugins that could just be malware, on a system that is easily compromised.
If you’re at all concerned about a russian hacker gaining access to your entire life, there is no situation in which you should be using OpenClaw. However, people are using it. Hundreds of thousands, in fact. So, let’s touch on some methods to at least make it less insecure.
1. Start with a more secure OpenClaw fork
Noting the inherent insecurities of OpenClaw, some alternative projects have emerged to address some of the issues. IronClaw and SecureClaw are of particular note. These tools introduce some missing security aspects of OpenClaw, such as:
- Sandboxing for untrusted tools, with capability-based permissions
- Credential encryption and protection avoid leaking secrets to third party tools
- Prompt injection defenses like pattern detection, sanitization, and policy enforcement
- Whitelisting to ensure only allowed sites are accessed
2. Put it on a different computer
This should be obvious but…dont give OpenClaw access to your personal computer or phone. It’s a recipe for disaster, exposing literally all of your personal information. There’s a reason the Mac Minis became so popular. So make sure it’s running somewhere else.
3. Use new/secondary accounts
Another obvious one, but you should set up separate accounts for your bot to use. Example: make a new email address for OpenClaw to use, don’t give it access to your personal gmail.
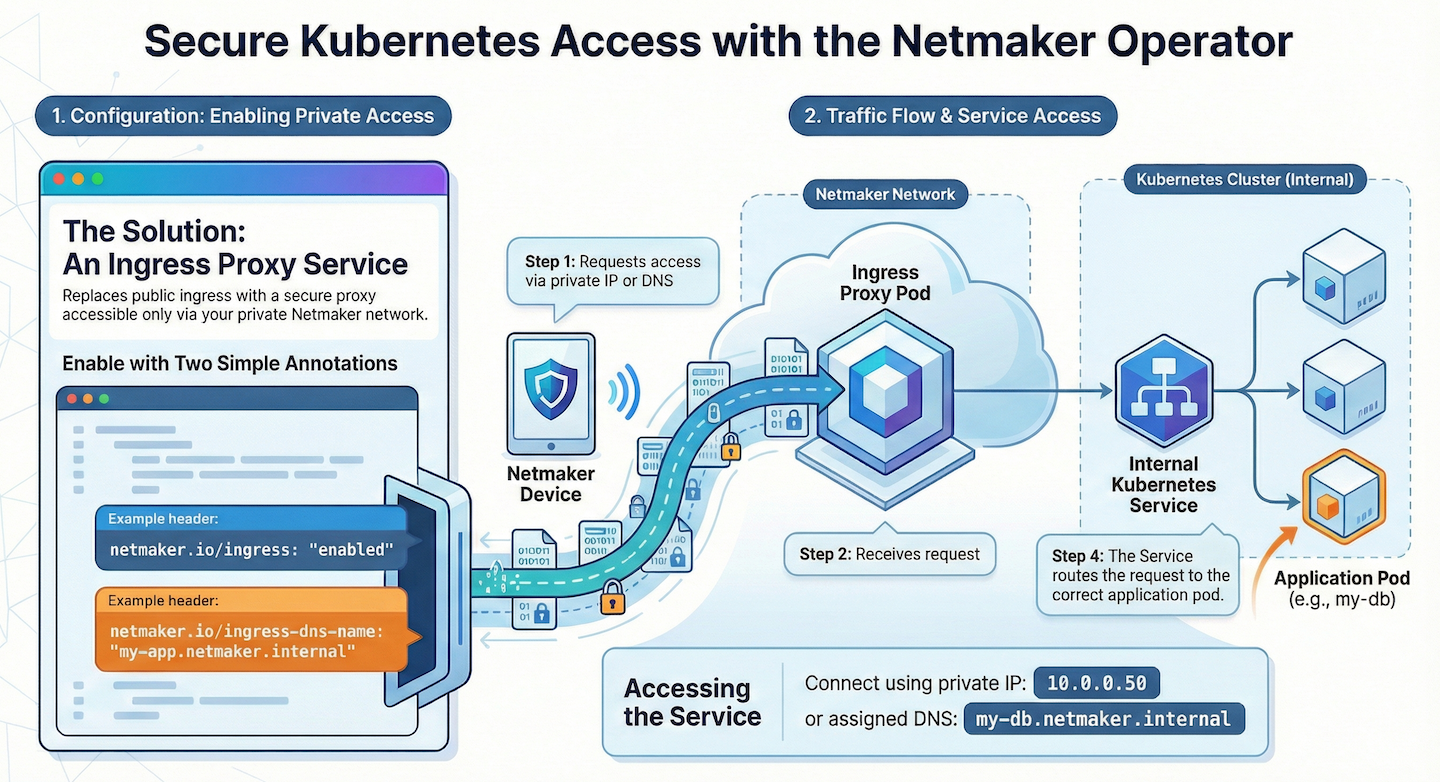
4. Keep the interface private
If someone can access your OpenClaw interface, they have the power to use it, and get access to all of your credentials / keys. So, make sure to keep that interface secured. You can even put it behind some secure remote access solution like *cough cough* Netmaker to ensure that only you have access.
Conclusion
These are in no way an endorsement of using OpenClaw. As a security-centric company, Netmaker recommends you stay away. But as in the real world, people are going to do unsafe things. So, if you’re going to do unsafe things, at the very least, do your best to avoid the worst case scenario.
.svg)





.svg)