Streamlining Remote Access for IT service providers

Let's face it. Managing remote access to your customers as an IT service provider can feel like a never-ending struggle. Traditional VPN solutions often leave IT teams drowning in complexity. Ever wrestled with cumbersome configurations, skyrocketing costs as your team and customer base grows, or that nagging feeling of vulnerability? You're not alone.
If you're a network architect, cloud engineer, CTO, or IT administrator tired of spending more time wrestling with remote access than actually getting work done, this article is for you. We'll explore the challenges you face and introduce a modern approach that streamlines efficiency and keeps your data secure.
The Challenges of Traditional Remote Access
While enabling remote access to client environments is empowering and can streamline your operations, traditional remote access solutions like VPNs (Virtual Private Networks) can introduce a hidden set of thorns.
Let's dig into the technical challenges that can leave your IT team feeling more like weary gardeners than architects of a thriving remote work ecosystem.
Costly Resources
Traditional VPNs often create a resource drain for
businesses. Here's the breakdown:
- Hardware: On-premise VPN solutions require dedicated hardware like VPN concentrators and firewalls. The installation, configuration, and maintenance costs can be significant, especially as your team and customer base scales.
- Software Licensing: Many VPN solutions charge hefty licensing fees (per user or connection). As your workforce grows, so do these recurring expenses. Licensing models can also have hidden fees for features like advanced encryption or multi-factor authentication.
- Maintenance: Keeping your VPN infrastructure running smoothly requires ongoing maintenance and security patching. It can mean additional IT staff hours or expensive managed service contracts to stay up-to-date on the latest vulnerabilities and apply patches promptly.
- Network Segmentation: Your customers expect their data to be secure and segmented from other customers, and that only appropriate team members have access. But access across different customer environments can be a big struggle to set up and maintain.
These combined costs can quickly eat into your IT budget, leaving less room for investment in other critical areas like cloud migration or security enhancements.
Configuration Complexity
Setting up and configuring a traditional VPN can feel like navigating a bureaucratic maze. Here's why:
Complex Protocols
VPN protocols like IPsec (Internet Security Protocol) and OpenVPN involve intricate configurations and firewall rule management.
These protocols rely on cryptographic algorithms to encrypt data and establish secure tunnels between devices and the network. However, misconfigurations can lead to security vulnerabilities or connectivity issues.
Remote Access Headaches
Granular access control lists (ACLs) specify which users and devices can access specific network resources. This process can be time-consuming and error-prone for IT administrators.
Limited Device Support
Traditional VPNs often struggle to support a diverse range of devices, especially mobile endpoints. Mobile devices may have different operating systems and security features than laptops, requiring additional configuration or client software installation.
The initial setup and ongoing management of a traditional VPN can consume valuable IT resources better spent on core business initiatives.
Limited Scalability
As your business thrives and your remote workforce expands, a traditional VPN can quickly become a bottleneck. Here's how:
- Limited User Capacity: Many on-premise VPN solutions have a fixed capacity for concurrent user connections, often limited by the VPN concentrator. When a surge in remote users occurs, exceeding this capacity can lead to performance issues like slow connection speeds and dropped connections.
- Geographic Restrictions: Traditional VPNs typically require users to connect back to a central location, which can introduce performance problems for distributed teams. Data packets travel to the central VPN server and back, increasing latency and impacting applications that require real-time responsiveness.
- Limited Split Tunneling: Split tunneling allows users to access specific resources remotely while maintaining a local internet connection for other traffic. However, traditional VPNs often have limited or cumbersome split tunneling capabilities.
A traditional VPN that can't scale with your growing team can hinder productivity and business growth.
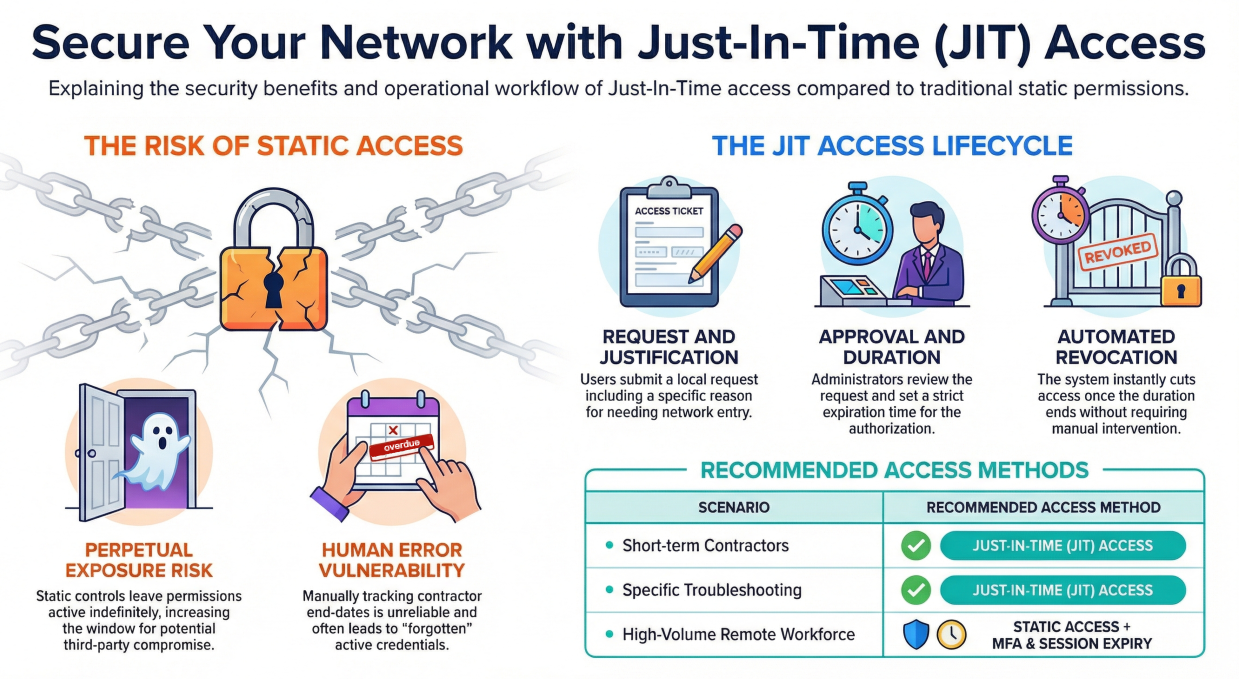
Security Vulnerabilities
Security is paramount when it comes to remote access. Unfortunately, traditional VPNs can introduce vulnerabilities:
- Single Point of Failure: If a hacker gains access to the VPN server, they can potentially intercept all traffic passing through the tunnel, putting sensitive data at risk.
- Weak Encryption: Older VPN protocols like PPTP (Point-to-Point Tunneling Protocol) have weaknesses in their encryption algorithms, making them susceptible to brute-force attacks. Weak encryption algorithms can be cracked with enough computing power.
- User Management Challenges: Traditional VPNs can make managing user credentials and ensuring proper access control hygiene challenging. IT administrators must manually ensure users choose strong passwords and enforce regular password changes.
- Segmentation issues: Improperly segmented virtual networks can lead to network perimeters that are too large or span multiple customers, a big problem for data security.
Security micromanagement can lead to user frustration and password fatigue, potentially increasing the risk of users resorting to weak or reused passwords.
Additionally, traditional VPNs may not offer multi-factor authentication (MFA), which adds an extra layer of security by requiring a second verification factor beyond just a username and password.
While traditional VPNs have served their purpose, they are no longer the optimal solution. Limitations in scalability, complex configurations, and potential security vulnerabilities can hinder your business growth and expose your data to unnecessary risks.
The next section will explore a modern alternative that tackles these challenges head-on, fostering a remote work environment that is both efficient and secure.
Benefits of Modern Remote Access Solutions
It's time to embrace the benefits of modern remote access solutions. These innovative approaches can overcome the challenges of a traditional VPN solution to create a thriving remote work environment.
Cost-effective and Scalable
Subscription-based pricing models eliminate upfront hardware and software licensing costs. You only pay for the number of users you need, making them highly scalable for growing businesses.
Cloud-based deployment removes the need for on-premise hardware and associated maintenance burdens. Cloud providers handle infrastructure management and security patching, freeing your IT team to focus on strategic initiatives.
Simplifying the deployment, configuration, and management of modern solutions translates into reduced IT overhead. Automated provisioning and intuitive user interfaces minimize the burden on your IT staff.
Easy Deployment and Management
Automated configuration wizards eliminate the need for manual configuration and minimize the risk of errors. Modern solutions typically feature user-friendly web-based interfaces that simplify management tasks.
These interfaces allow IT administrators to easily configure access controls, monitor user activity, and troubleshoot issues. Some solutions include self-service portals for user tasks like password resets or device enrollment. These added features improve the user experience for remote employees while reducing the workload of IT staff.
Increased Security with Advanced Encryption and Access Controls
Modern solutions use strong encryption algorithms like AES-256 to ensure the confidentiality of data in transit. These algorithms are virtually impossible to crack with current computing power.
Multi-factor authentication (MFA) or biometric access adds extra security, requiring a secondary device, fingerprint, or face scan. With this extra layer, the risk of unauthorized access attempts is significantly reduced.
Network segmentation and point-to-point access controls mean that only explicitly authorized devices and groups have access to each other..
Seamless Integration with Cloud and On-Premises Infrastructure
Many solutions are built with a cloud-native architecture, seamlessly integrating with popular cloud platforms like Microsoft Azure, Amazon Web Services (AWS), and Google Cloud Platform (GCP).
Single Sign-On (SSO) allows users to authenticate once and access all authorized applications and resources, regardless of their location or whether they are cloud-based or on-premises. This improves user experience and reduces the risk of password fatigue.
Modern solutions often integrate with Identity and Access Management (IAM) solutions, providing centralized control over user identities and access privileges across your entire IT infrastructure.
Improved Productivity and Collaboration
Effective remote access systems empower employees to work from anywhere with an internet connection and the appropriate device. Modern solutions offer broad device compatibility, allowing employees secure access to resources from laptops, desktops, tablets, and smartphones.
This flexibility empowers a truly mobile workforce. The simplified user experience and self-service capabilities of modern solutions minimize disruption and improve overall user satisfaction, translating to a more productive and engaged remote workforce.
Cultivating a Thriving Remote Access Environment with Netmaker
The limitations of traditional VPNs can hinder your business growth and expose your data to unnecessary risks. Modern remote access solutions offer a path forward, fostering a secure and efficient work environment between your employees and customers.
Among the available solutions, Netmaker is a compelling option for IT service businesses seeking a modern approach to remote access. It addresses the key challenges we've discussed, offering a cost-effective and scalable solution with features like:
- Mesh VPN: For secure and high-performance remote connections.
- Remote Access Gateway: A convenient way to provide remote access to your network with minimal setup.
- Network Segmentation: Deploy different networks for different customers to keep data secure and separated.
- Granular Access Controls: Ensuring only authorized users access specific resources.
- Seamless Cloud Integration: Integrating with popular cloud platforms and IAM solutions.
- Enhanced Security: Utilizing strong encryption and MFA.
- Simplified User Management: Automating deployment, configuration, and user management.
By adopting Netmaker, you can empower your remote workforce with secure and efficient access to the resources they need, fostering increased productivity and collaboration. We encourage you to explore Netmaker and discover how it can enable a secure remote work environment for your business.
Visit our homepage to learn more about our features, pricing plans, and how Netmaker can help you unlock the full potential of your remote workforce.
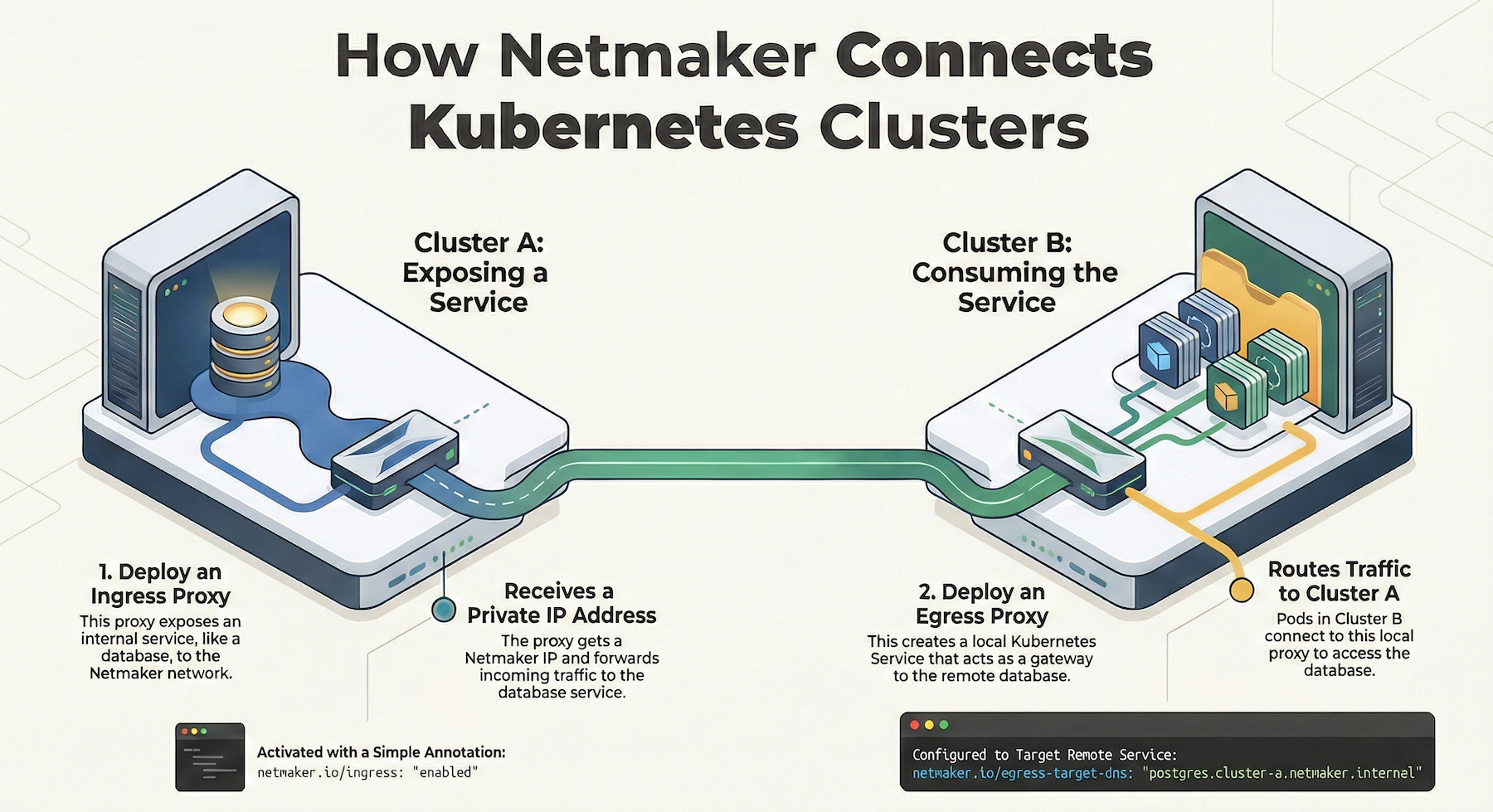
Enhancing Remote Access with Netmaker
Netmaker offers a modern solution to the challenges faced by IT service providers in managing remote access. By utilizing advanced mesh networking technology, Netmaker significantly reduces the complexity associated with traditional VPNs. It provides seamless integration into existing infrastructures, allowing IT teams to efficiently connect remote devices without the need for costly hardware or complex configurations. The platform's ability to run within containers like Docker or Kubernetes further simplifies deployment and maintenance, reducing the burden on IT resources.
In addition to cutting costs, Netmaker enhances security through automated network management and end-to-end encryption. Its multi-tenancy capabilities ensure network segmentation, allowing IT service providers to securely manage multiple client environments while maintaining strict access controls. With Netmaker, IT professionals can focus more on their core tasks and less on troubleshooting connectivity issues. To get started with Netmaker and transform your remote access strategy, sign up at Netmaker.
.svg)





.svg)